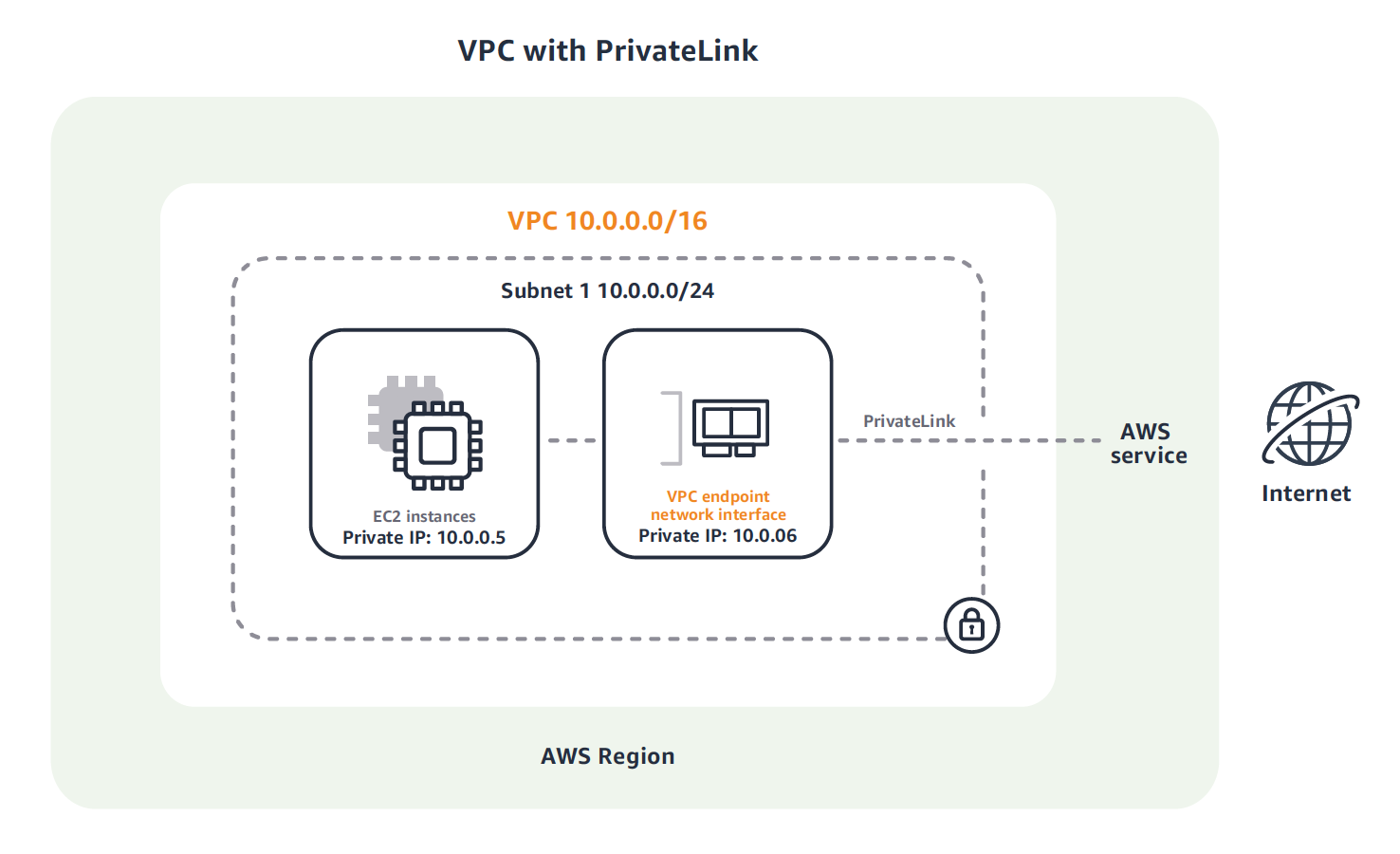
When using PrivateLink, clusters can be connected just as if they were living inside a VPC. CloudAMQP creates an Endpoint Service to connect the VPC, creating a new network interface used to communicate with the cluster.
As if this wasn’t simple enough, the interface created inside the VPC gets a private IP and if private DNS is enabled inside the VPC, the same hostname can be used as normal and the cluster will now point to the new network interface. This means that an application can be moved in and out of the VPC and without any configuration changes. Once moved, the application will automatically use the private secure connection to CloudAMQP.
 Source:
Amazon Virtual Private Cloud Overview
Source:
Amazon Virtual Private Cloud Overview
How to enable PrivateLink
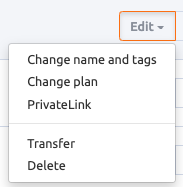
To enable PrivateLink, go to the CloudAMQP Console and the list of instances. Click Edit next to an instance and then PrivateLink.
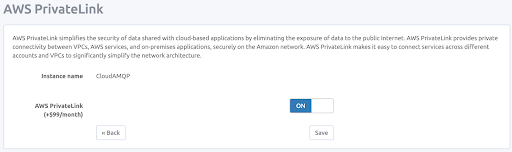
This screen displays the option to enable AWS PrivateLink. Don’t forget to click Save.
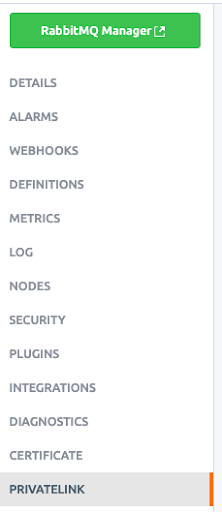
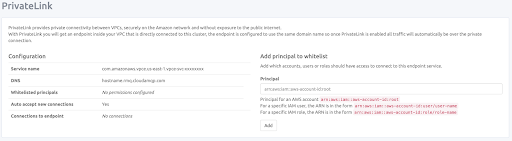
Once enabled, a new menu item will appear called PrivateLink, that includes all configuration settings.
It only takes a minute to activate PrivateLink, which displays the screen below. If all the fields are not displayed, it is not activated completely. In this case, allow for about one minute before refreshing the screen and all the fields to become active.
The only configuration needed is the principal for an AWS account in the format
arn:aws:iam::aws-account-id:root.
For a specific IAM user, the ARN is in the format
arn:aws:iam::aws-account-id:user/user-name
For a specific IAM role, the ARN is in the format
arn:aws:iam::aws-account-id:role/role-name
Once the new PrivateLink has been activated, create an Endpoint for it in your AWS account. If using the AWS web interface, click the radio button 'Find service by name' and paste the Service Name shown in the PrivateLink view of the CloudAMQP console. Click the 'Verify' button in the AWS console to verify that the PrivateLink service exists. Then select the VPC in your account that is to be connected to the CloudAMQP instance.
As of this writing, AWS does not support cross-region PrivateLinks. Please ensure that the CloudAMQP instance and the VPC that will connect to it are in the same AWS region.
If your VPC is configured to enable DNS support, check the box to enable DNS name for the endpoint. In this case, you will see the CloudAMQP hostname listed in the Private DNS name section of the details view for the PrivateLink endpoint.
If your VPC cannot enable DNS support, amqp clients will need to use the AWS-provided DNS name to connect over PrivateLink. Alternatively, to enable the DNS configurations for your VPC, follow these steps:
- Enable DNS resolution on your VPC (enableDnsSupport)
- Enable DNS Hostnames (enableDnsHostnames)
- Your EC2 instances must use the Amazon resolving DNS servers, which are typically communicated to the EC2 instance using the VPC DHCP Options
- When you have created the VPC Peering Connection between your VPC and the CloudAMQP VPC, you must enable support for DNS resolution
Once these 4 steps have been completed the CloudAMQP hostname can be used by instances connecting via PrivateLink.
To complete the Endpoint creation, click the 'Create endpoint' button at the bottom of the form in the AWS console. PrivateLink should now be ready to use, and clients should be able to connect to the CloudAMQP RabbitMQ server.
The ports on the CloudAMQP instances that are open via PrivateLink are 443, 5671, 5672, 1883, 8883, 61613 and 61614. Other ports can be opened upon request.
Pricing
If VPC is already enabled, there is no additional charge for PrivateLink. To add PrivateLink without previously having a VPC, the charge is $99 per month. If PrivateLink is disabled for any reason, there will only be a charge for the time it has been active.
For more information on AWS PrivateLink, go to AWS.
Please email us at support@cloudamqp.com if you have any suggestions, questions or feedback.






